
The Cyber Research Center (CRC) is one of three research centers in the Department of Electrical Engineering and Computer Science. The research centers exist to provide opportunities for development to both cadets and faculty, above and beyond the curriculum. The CRC focuses on opportunities and research that span the entire continuum of cyberspace operations.
CRC Mission:
To educate and inspire cadets in cyberspace operations, find and sustain margin of excellence opportunities for cadets and faculty, and build and maintain ties with the Army and national cyberspace operations community to develop the skills necessary to fight and win in the cyber domain
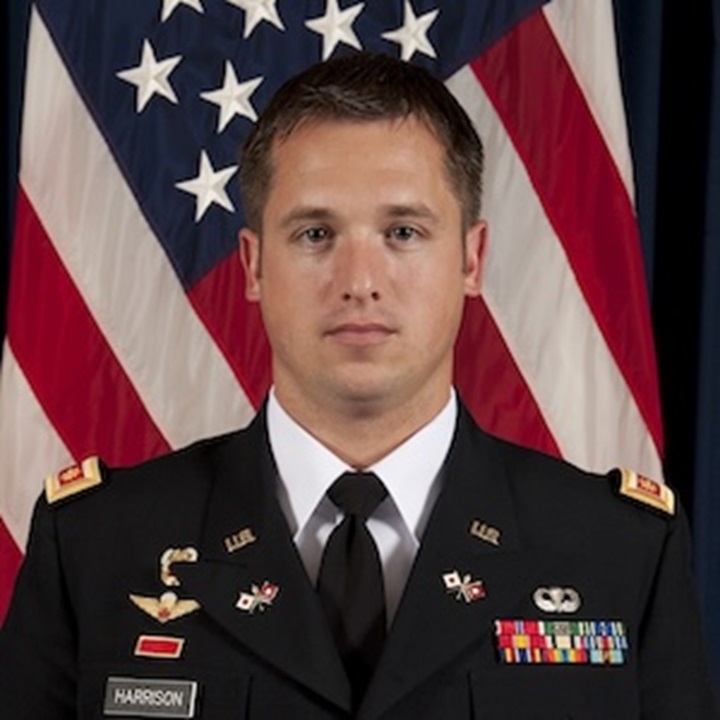
COL Rob Harrison graduated from West Point in 2003 and received a master's degree in engineering and a doctorate in computer science from Princeton University. He has served in multiple assignments as a Signal Corps officer and network systems engineer (FA26A) in both conventional and special operations units. He has deployed three times in support of Operation Iraqi Freedom.
He is a graduate of Airborne School, the Signal Officer Basic Course, the Signal Captain’s Career Course, the Telecommunications Systems Engineer Course and the Command and General Staff Officer Course. His research interests include programmable network hardware and software, network routing and management, and cybersecurity.






U.S. Military Academy
Official Mail and Distribution Center
ATTN: MADN-EECS CRC
646 Swift Road
West Point, NY 10996-1905
Phone: (845) 938-5537
The CRC research program integrates faculty and cadet efforts to solve both academic and real-world problems. The CRC works with a variety of government, industry, and academic partners.